Your staff are working remotely but are they working safely?
By Anna Gonzalez
24/11/2020
This year’s coronavirus pandemic has seen many traditional workplaces close causing millions more workers to operate remotely – many for the first time. So as we enter this new phase of ‘Working from Home’, it would be a good idea to pause and consider what (if any) the increased risks to our cybersecurity may be, and what we can do to hunker down and stay safe.
Certainly, those workers who are using a personal device for business purposes should ensure they take some extra precautions to help keep both personal and business data secure.
Vishing
If you’re anything like me, you’ll have rediscovered you have a landline, which may be subjecting you to a threat vector otherwise missed when you’re in the office. The primary threat is known as ‘vishing’, which takes everything we love about a Phishing email and transforms it into a phone call. Scammers will claim to be from your cable provider (Virgin, Sky etc.) and ask if you have experienced issues with your connection. They claim to be from the technical team and “can definitely help you with your speed issues if you are near a computer”. I followed their instructions on my last call (for investigative purposes) and discovered they will ask you to log-in to your device and follow commands to allow them to gain remote access to your device. At this point, they will proceed to install all manner of malware, keystroke loggers (to steal passwords), Ransomware etc. Remain vigilant in the face of vishers – Sky have been targeted with a number of vishing campaigns recently, so always call your suppliers directly!
Malicious texts
Alternatively, your telecoms providers (EE, O2, Vodafone etc.) may send you a text message to advise there has been an issue with your payment – with a link. Just because it is a text message does not mean it is safe and of course these messages do not always originate from the companies they purport to be. Be sure to connect to your account via a homepage or call customer support directly. Beware of these malicious texts – messages claiming to be from EE & Vodafone have been doing the rounds recently.
PayPal phishing emails
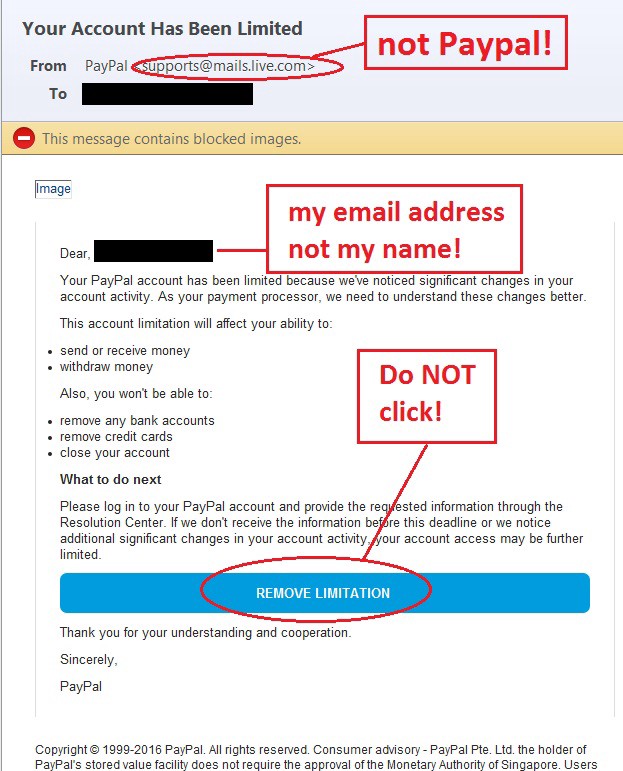
The good, old-fashioned phishing email has been evolving recently to become even slicker. I have seen an increase in PayPal emails with variants on the theme of “fraudulent activity… your account with be closed forever”. Clearly these messages are designed to panic you into action. I have included below an example of what to look out for. Note that if you use a Password manager you may find that every so often you get stuck in a ‘captcha loop’. You will need to copy your password manually and this should fix the issue. Most importantly, do not be tempted to click on a well-timed email that is more than likely not from PayPal.
Things you can do to keep yourself secure – a handy to-do list!
1. Awareness & user training. Social engineering remains the main way into a network (large and small) with humans proving the weakest link. Talk to us about how to create a plan, how to test employees in a safe environment and how to support them in understanding threats and implications.
2. Password managers. Social engineering remains the main way into a network (large and small) with humans proving the weakest link. Talk to us about how to create a plan, how to test employees in a safe environment and how to support them in understanding threats and implications.
3. Secure solutions. Products like SOPHOS InterceptX, O365, DarkWeb Scanning and SonicWALL can ensure you are well protected against a variety of threats whether you are in the office or WFH.
4. Mobile security. This becomes ever more important as threats continue for both business and personal users.
5. Patch, patch, patch! Check your home and work devices regularly for any new patches (Microsoft Patch Tuesday is a good day to check). Ensure you have up-to-date antivirus software on your PC, laptop and mobile device and, if in doubt, run a scan. If you use SOPHOS, ask us about their free Home Premium Licences available to all your users.
6. 2FA and Multifactor Authentication. This remains a highly recommended measure that everyone should be applying any application wherever possible.
7. Secure connections. Ensure your users are connecting to the office via a Virtual Private Network and that they know how to secure their home routers – these should be password protected and WPS disabled!
8. Sharing is caring. Create an open environment for users to share any worrisome emails, texts, or generally dubious activity without fear of repercussions. When someone inevitably clicks on a link, the sooner it is flagged the more chance you have of isolating it from other parts of your network.
9. Create an internal Playbook. What would you do if you suffered a breach? Who in your team needs to be involved and what are your processes? We can help with specific courses for GDPR and Cybersecurity.
10. Scan, scan, scan! Talk to us about regular vulnerability scanning and possibly penetration testing. We can help you understand which holes the bad guys can leverage and what you need to do to become more secure!
There is one final thing we can all do in the fight against malicious emails. NCSC have introduced a pioneering suspicious email reporting service, which allows you to forward any email you suspect may be harmful to report@phishing.gov.uk
Stay safe out there and, if you have any concerns, do reach out. We are always happy to offer you our expert advice and best practice security knowledge.
Contact Utilize

